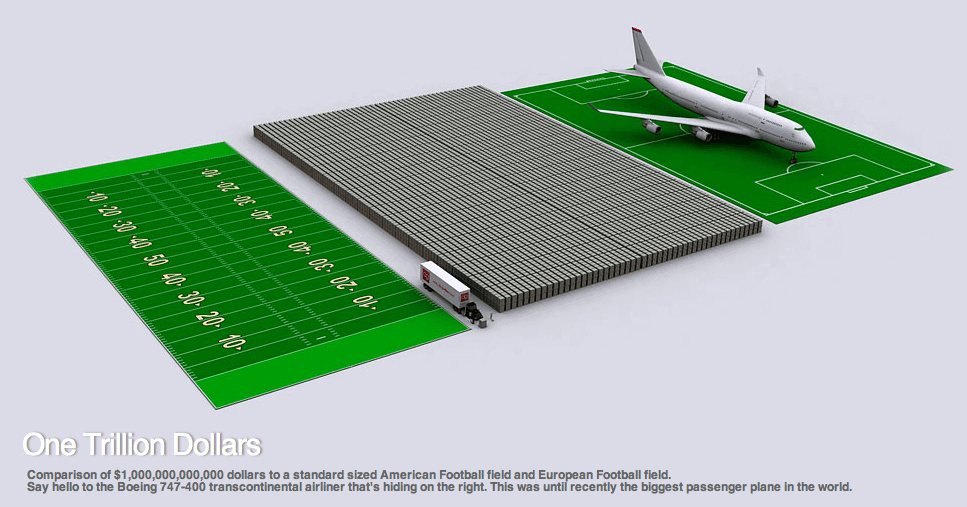
According to the Huffington Post, a trillion dollar bills, placed on pallets and stacked two pallets high, would be as long as and wider than a traditional U.S. or European football field — and consume far more space than a Boeing 747-400 transcontinental airliner.
This illustration helps us comprehend the scope and breadth of the escalating problem of cybercrime that all organizations face today. Far from the days of simply infiltrating unsuspecting email users’ accounts with spam — although that does still happen — larger and more sophisticated attacks negatively impact corporate mergers and acquisitions, compromise personal healthcare privacy, and cost untold amounts in both reputation and cold hard cash.
Start application security early.
With much at stake for businesses — and their customers — having the right security strategy is imperative to minimize risk, as well as cost. More than a billion web applications provide access to business data for employees and customers, making application attacks a primary concern in all industries. For security company F5 Networks, protecting applications and the data behind them is the focus.
It used to be that application security was something considered after initial application development. F5 saves organizations time and money by offering security solutions that can be integrated into applications at the design stage. These work with a range of powerful, integrated solutions that can identify and protect against threats before they reach the app.
For organizations considering next-generation data centers, any kind of cloud application or cloud provisioning, F5 provides speed, reliability and portability. “We’re really in the sweet spot, because we have all three,” says Preston Hogue,senior director of security marketing at F5. “Portability is uniquely important in the cloud; it allows the same security controls developed for the data center to travel with the app to the private or public cloud.”
F5 security solutions
F5 Networks came from the applications world and got into the security market based on performance and reliability. “We know how applications should run,” Hogue adds. While other companies are “pure-play security,” F5 does more to support the entirety of apps. “When you’re on the web, we’re one of the last lines of defense around the applications for protection, and also ensuring that the right people are getting the right information, and that it’s secure, fast and reliable.”
F5 technology ensures that when a page is requested from a web application, the company hosting the application can manage that connection to make sure the page stays live regardless of the data center or server it needs to go to. Whether data is on premises or in the cloud, F5 supports any infrastructure, thanks to its many technology alliances, including Amazon Web Services (AWS) and Microsoft Azure. This means data is protected even in a hybrid environment with built-in capabilities that eliminate the need for additional products or management consoles.
Specializing in applications also enables F5 to develop ways to deflect Distributed Denial of Service (DDoS) attacks. According to Hogue, “One of the biggest ways hackers gain access to a network is to launch a DDoS attack. … DDoS protection is key in making sure apps remain available and your business keeps running.”
While other companies keep connections in a table, making a best guess about “conversations” without actually intercepting communication between clients and servers (also known as stateful technology), F5 is full proxy. This allows information going from the client to the server to be fully inspected, redirected to the cloud or stripped of anything malicious before being connected or redirected. The old argument against full proxy was that it’s slow, but F5 has developed the ability to complete tasks at carrier speeds.
Another concern is over availability and control inside encrypted pages. Now that websites are moving from, for instance, only having a credit card transaction page encrypted, they’re becoming fully encrypted. But it’s very difficult to protect what you can’t see. F5 provides visibility and data control by using some of the most sophisticated ciphers — algorithms that confirm the identities of both client and server — built into that “communication handshake” when a client reaches out to a server. The ciphers operate according to F5’s “secure, fast and reliable” methodology, securing the transaction, boosting speed and maintaining uptime.
How Insight helps
Insight offers the expertise required to strategize, design and implement technology solutions to help businesses manage today’s evolving workforce. Insight also has deep relationships with industry-leading technology partners and is in a unique position to help organizations that are building new data centers, moving to the cloud or creating a hybrid architecture.